Building a social cyber community of interest - lessons from the field
Content led communities for the 2020s to hit Gen Z with a dash of brand recognition
Backstory
As a Group CTO for a services company I describe my job as existing in thirds:
1/3 being the executive responsible for Research, Product & Development for my employer.
1/3 being the executive the technologists at the firm recognise as looking after their interests and who they can engage with and be supported by.
1/3 engaging with stakeholders, customers or employees be they past, current or future to provide value.
It is with the last of these in mind in the winter of 2017/2018 I set out on an experiment to see if I could build a cyber community of interest that provided value.
Armed with 20 dollars investment for ‘internet points’ and a rough plan I started.
This is the journey and lessons that I learnt along the way.
If you enjoy it, I encourage you to sign up to my irregular CTO musings:
If you value it, I encourage you to share it:
Information-opolies
In cybersecurity we’ve always had a very vibrant offensive research community, indeed it was my exposure in the mid-90s that solidified it as the career of choice. As the community has grown over the years the sharing of new research, capabilities, vulnerability writeups, tooling and exploits has increased dramatically. But it only took 30 or 40 years…
In the cyberdefence community whilst some of this was happening in 2017 there were a number of key dominant players in the commercial ‘threat intelligence’ space. As a competitor to these firms I could see some of the value but you could also see rich house and poor house starting to emerge in cyber defence.
We had lots of operational folk who were busy, stressed and struggling to stay on top of what information was out there that could help them if they couldn’t afford the services. Similarly we had a growing cadre of defensive security researchers sharing operationally useful information on platforms like Twitter which wasn’t hitting the desks of incident responders, threat intelligence analysts, malware analysts or operations teams who would benefit.
Around the same time I was also becoming increasingly frustrated with the moderation and quality of posts on /r/netsec on Reddit after having joined up in 2013. Posts I thought were useful were being moderated out or down voted.
So how do we solve the problem, provide value and have impact?
Meta is supremely useful
We will all recognise the Internet is vast and the content on it growing exponentially. Cyber research and all the associated subdisciplines along with the resulting content is just one example of that.
I’ve always found ‘meta’ supremely useful be it /. in the old days or more recently Hacker News, Reddit or Lobsters etc.
Beyond these I’ve experimented with the likes of Feedly, Twitter lists, Twitter super aggregators, RSS, Huginn and similar to keep on top of the topics I’m interested in.
I’ve also over the years been inspired by the likes of Haroon Meer at Thinkst and their ThinkScapes research aggregation product.
So this got me thinking which resulted in a thesis of…
… we could crowd source the content, help each other whilst build a community. This would have a side benefit of a content led marketing like approach to raising awareness of my employers brand by association.
But what platform? Blog - nope, a little too much 2000s. Twitter - nope, too constrained. Reddit seemed to be the perfect mix of curation, crowd sourcing and customisation to build a community on.
The community that took three years
So in the winter of 2018 (January) I took the plunge and started to build on Reddit /r/blueteamsec . Its name was unoriginal and named after the /r/netsec/ (one of the original security home on Reddit) and /r/redteamsec/ (founded the summer before for Red Teams). Funnily enough someone latterly created /r/purpleteamsec/ in February 2020.
In the early years (the first two) there was very few of us, but we grow. I built the community using a very simple set of steps:
Clear rules - no high-level abstract news or marketing
Strong moderation to keep signal/noise levels right.
Finding useful content and using it as an overflow brain for useful things.
Cross-posting to more popular ones in a form of internal Reddit advertisement to grow the user base.
Over time I refined the model and the community to create a high quality space and incentivise participation :
Blocked cross-posting into subreddit to keep us as a golden root source of information.
Added post flair to categorize the content across different cyber defence tradecraft elements - discovery, defence, vulnerability, exploitation etc.
Added user flair to recognize those community builders.
Awarding extensively using internet points on Reddit (gold, silver etc.) to contributors of great content as a thank you.
This started to have an effect, but as mentioned the first couple of years were meagre.
3,500 December 2019
So this was nearly two years and we’d grown to about 3,500. 2020 was an amazing year for a couple of reasons, firstly the pandemic but secondly we had a set of major security events. It was during this time I experimented with running ‘live’ posts aggregating information (meta again) from around the Internet associated with the event providing defensive teams a single source. This mainly involved using our own internal cyber defence, research and threat intelligence capability coupled with watching Twitter and quality checking.
Examples of such posts included:
January 2020 - Multiple Exploits for CVE-2019-19781 (Citrix ADC/Netscaler) released overnight - prepare for mass exploitation
January 2020 - CVE-2020-0674: Microsoft Internet Explorer 0day - Scripting Engine Memory Corruption Vulnerability being exploited in the wild
This approach wasn’t my first rodeo. It was based on previous experiments on other events in 2017/2018 and we have subsequently seen other vendors adopt similar approaches.
But it worked. These live posts really seemed to kick us up a gear in terms of membership
8,300 July 2020
On reflection you can see why - timely meta information which is updated in one place that you just need to refresh to stay current as the world around you is on fire.
We had a model, a growing community and people were starting to value it..
Rinse and repeat
With a model in hand that worked I just kept chugging. I recently documented the sources and methodology to provide the content on the Subreddit.
Today I probably contribute about 60% to 70% of the content in any given week. But that is still to me is amazing. We have a formula, it works and it’s all trending in the right direction across growth, awareness, community involvement and increasingly recognition from the community as to its value.
The community keeps growing
The community continues to keep growing.. the below is from a snapshot of traffic taken from Reddit on August 31st, 2021 (when I started writing this article). We can see the traffic growth over the year prior.
When we look at the unique it is fair to say it is less impressive in terms of growth, but still up between 10% and 20% year on year.
Network effect of membership
We can see the user base also continues to grow as the network effect starts to kick in.
To contextualise this growth this is what we’ve seen in term of the numbers (I had to use the Wayback machine so its got gaps):
1 subscriber January 2018
3,500 subscribers December 2019
8,300 subscribers July 2020
15,100 subscribers May 2021
17,700 subscribers August 2021
This isn’t Amazon of Microsoft levels of growth, but for small corner of the internet related to a niche topic it is less than terrible.
The Substack experiment
So that brings us to summer of 2021 and the next phase of the experiment / journey. I was reflecting that Reddit was awesome but it was still pull (or maybe push if you had setup RSS or similar).
For busy teams or maybe those not living it day to day pulling on Reddit and getting the so what was difficult. So enter the meta-meta Substack concept.
I was personally increasingly valuing various substacks being pushed to my inbox including cyberweekly by Michael Brunton-Spall on a Sunday. I looked at the Subreddit and wondered if we could use the content base, do some curation and analysis and push a substack to reach a new audience.
The model was simple. Each week I would summarize the key posts, provide the so what, do a little analysis and link to the original source if people were interested. Two weeks ago I went live with the first post which was promoted on Twitter and LinkedIn.
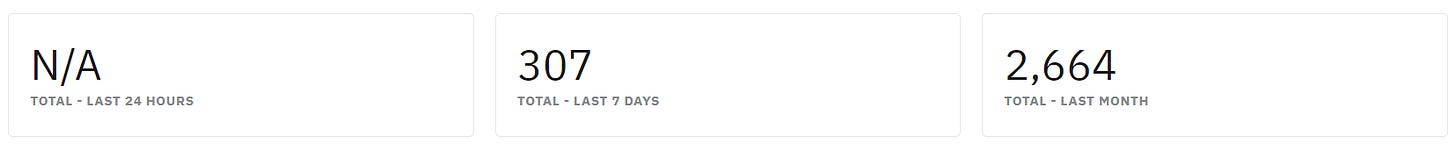
In the first two weeks I’m pretty happy with what we’ve achieved. Below is the number of subscribers.
The open and click rates aren’t too shabby either:
It is also reaching a new audience and engaging with folk in ways I didn’t expect. Also total hats off to Substack their management information is top of the class.
If you are interested the substack is the bluepurple and can be found here:
Reflections and lessons
It’s funny reflecting on projects such as this and the lessons from it.
Above all else have clear purpose and provide value/impact to the community you are trying to serve and everything else will be golden.
You need people who know the topic they are curating well (sorry social community media people).
You need to spend time every day to find the content with very little feedback or validation in the early days/months/years.
Promoting across social media channels e.g. Twitter, LinkedIn or Reddit itself might help accelerate awareness but it can still take years to get into a groove.
I’m of the view we could build many more of these sub-communities using a similar model for many facets of cyber security and beyond.
Two further reflections/things:
the Reddit ‘karma farming’ accusations in the early days/years was just odd - people would say I was karma farming whilst we were building the community by posting others content. The magic internet points I can tell you are not enough to keep you going alone.
when we launched the Substack the Reddit community reacted with suspicion questioned if they were just going to be spammed - I had to reassure them they were not.
In closing just keep giving the value to others without expectation (as Haley Joel Osment taught in Pay It Forward) and it will all come good but it might take a few years: